IAM Challenges for Hospitals and Healthcare Providers
Healthcare institutions rely on cutting-edge technology to provide top-tier medical care, including digital systems for managing patient data. However, this reliance also introduces new security risks. Hackers increasingly target healthcare organizations, with ransomware attacks on hospitals nearly doubling since 2022. Hospitals must act now to bolster cybersecurity and avoid costly breaches that threaten to disrupt patient care.
Protecting Private Health Information Under HIPAA
To ensure compliance with HIPAA, healthcare providers must implement strict access controls to ensure data privacy. With high turnover rates, managing hundreds of user accounts in medical facilities requires automated solutions that reduce the burden on IT departments, ensuring staff can only access data they need. Centralized access governance helps ensure HIPAA compliance and the safety of patient information.
Cybersecurity Standards in Healthcare
IGA Solutions Compared
Dive deep into the advantages and disadvantages of different available solutions for Identity Governance & Administration.
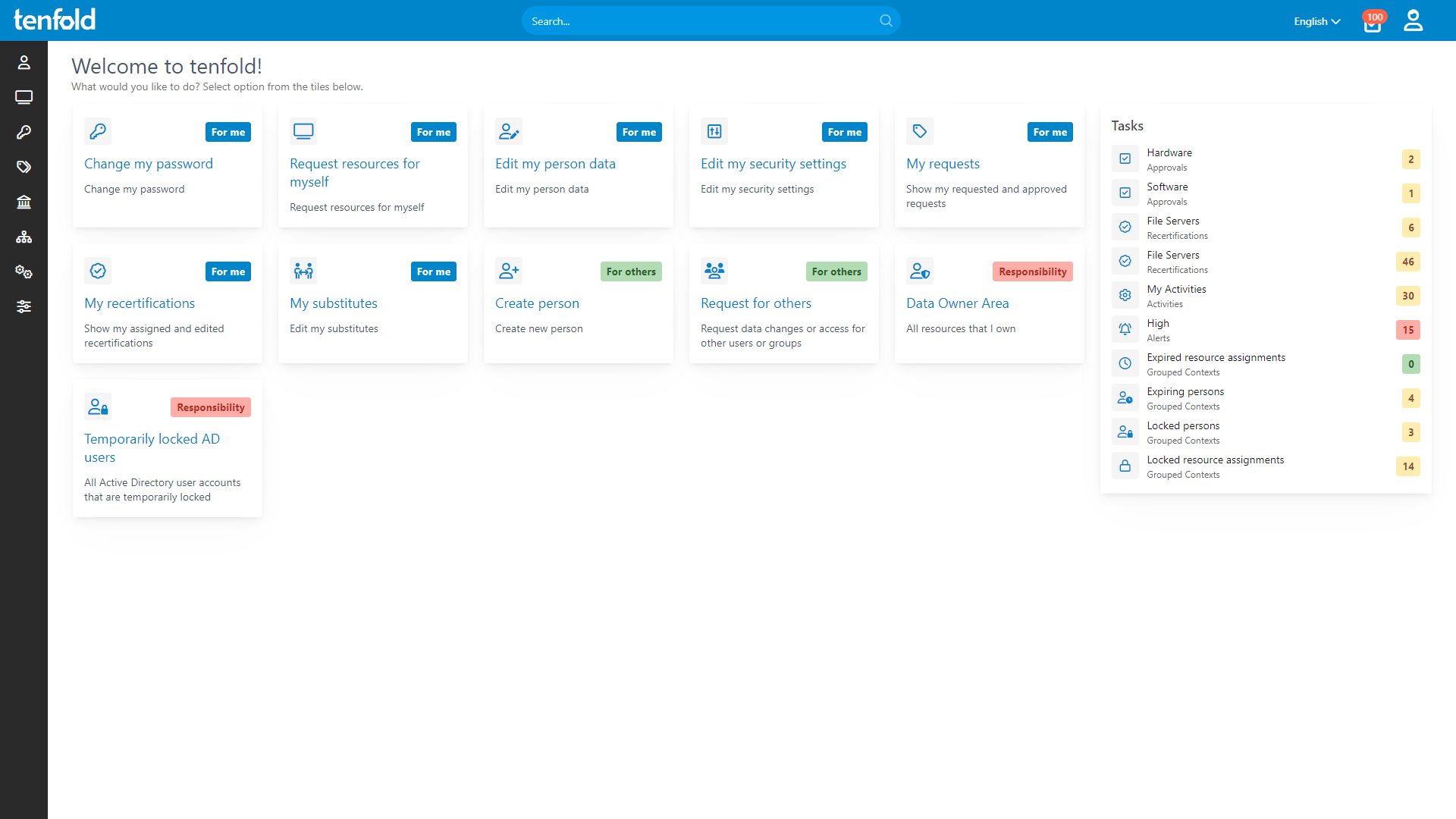
Governance Simplified
tenfold automates routine access governance tasks with ease. Using role-based access control, it automatically adjusts user rights when employees change roles or leave the organization. Leverage no-code plugins to quickly integrate everything from Active Directory and Microsoft 365 to common workplace and industry-specific apps.
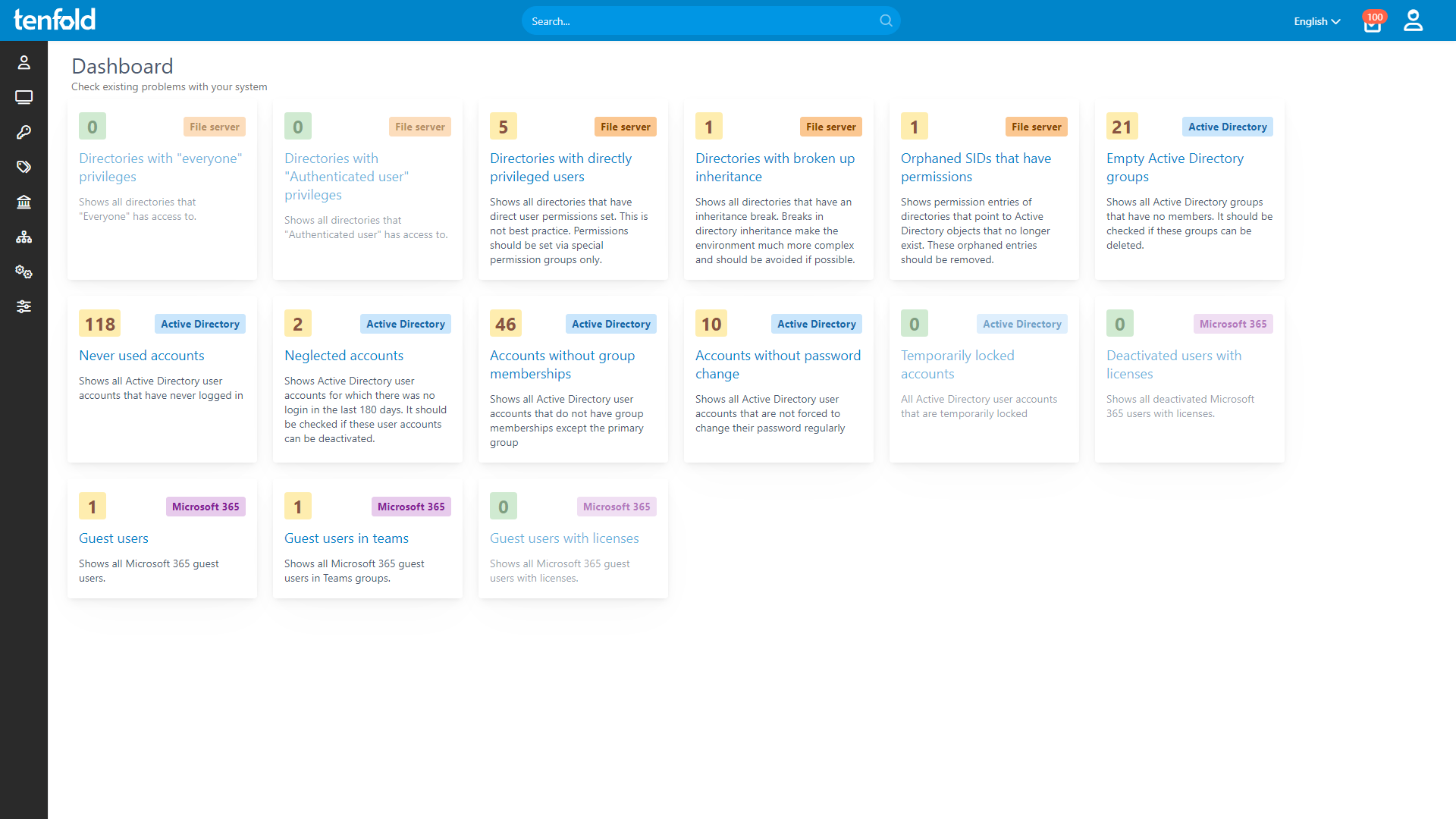
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.
Streamlined Security & Compliance
tenfold assigns access rights according to the principle of least privilege – a cybersecurity best practice and HIPAA requirement that minimizes the risk of unwanted access. With customizable approval workflows, detailed change logs, centralized reporting and streamlined auditing, tenfold allows healthcare organizations to maintain compliance with ease.
See how it works
With full visibility, central auditing and lifecycle automation, tenfold helps you regain control of IT privileges.
Watch our video overview to see it in action.
See tenfold in Action With Our Feature Video
Schedule a Live Demo With One of Our Experts
Put tenfold to the Test With Our Free Trial!