What Does the Generic Connector Plugin Do?
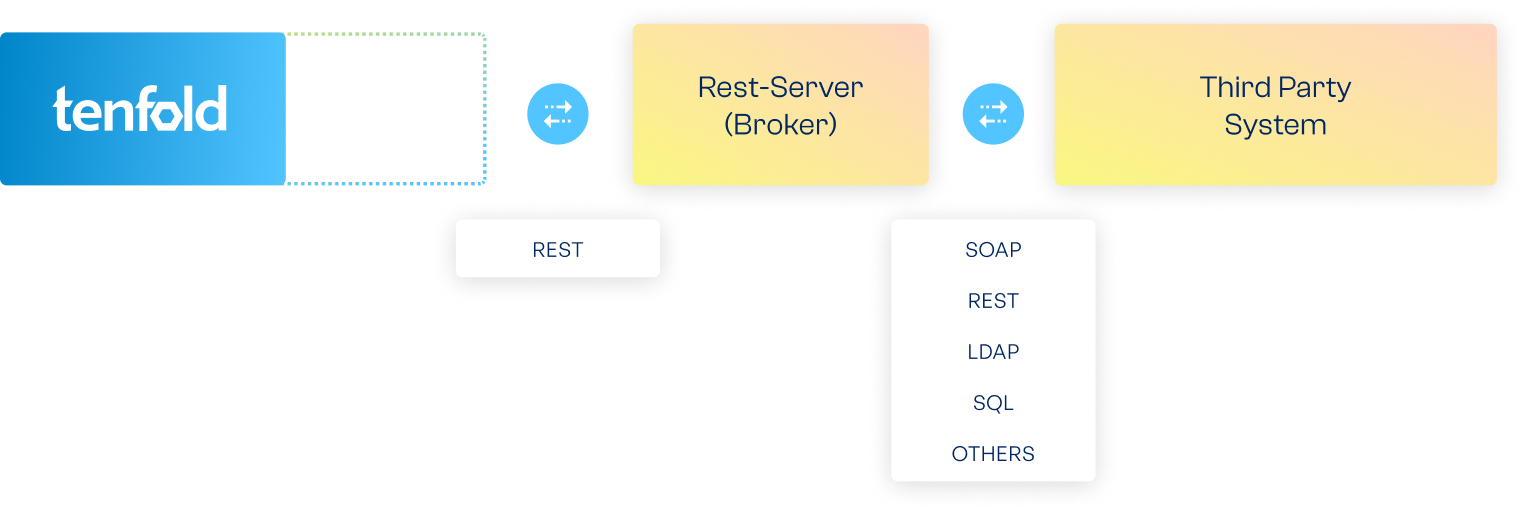
The Generic Connector can be used to connect applications to tenfold for which there is no pre-built plugin available (such as self-developed apps). A REST client within the Generic Connector acts as the client side of a REST API, as described in YAML/JSON.
To dock onto the Generic Connector, you must set up your own REST server. This acts as a broker between tenfold and the third-party system. The REST server implements commands sent by tenfold to the third-party system (and vice versa) via the designated API, e.g. SOAP, REST, SQL or proprietary interfaces.
Via the REST API, tenfold can control all functions related to the management of users and access rights. More information about using the Generic Connector can be found in the tenfold documentation. For specific questions about individual apps, please do not hesitate to contact us directly.
Enterprise Edition
System Requirements:
The integration of third-party systems requires the implementation of a corresponding REST server which is not provided by tenfold.
tenfold in a Nutshell
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.