How Does tenfold Manage Exchange Online Permissions?
The tenfold Exchange Online Plugin makes it easy to both assign and track permissions, providing you with a clear overview of who has access to specific mailboxes and mailbox folders. By breaking down nested groups, tenfold also shows you the effective permissions held by users.
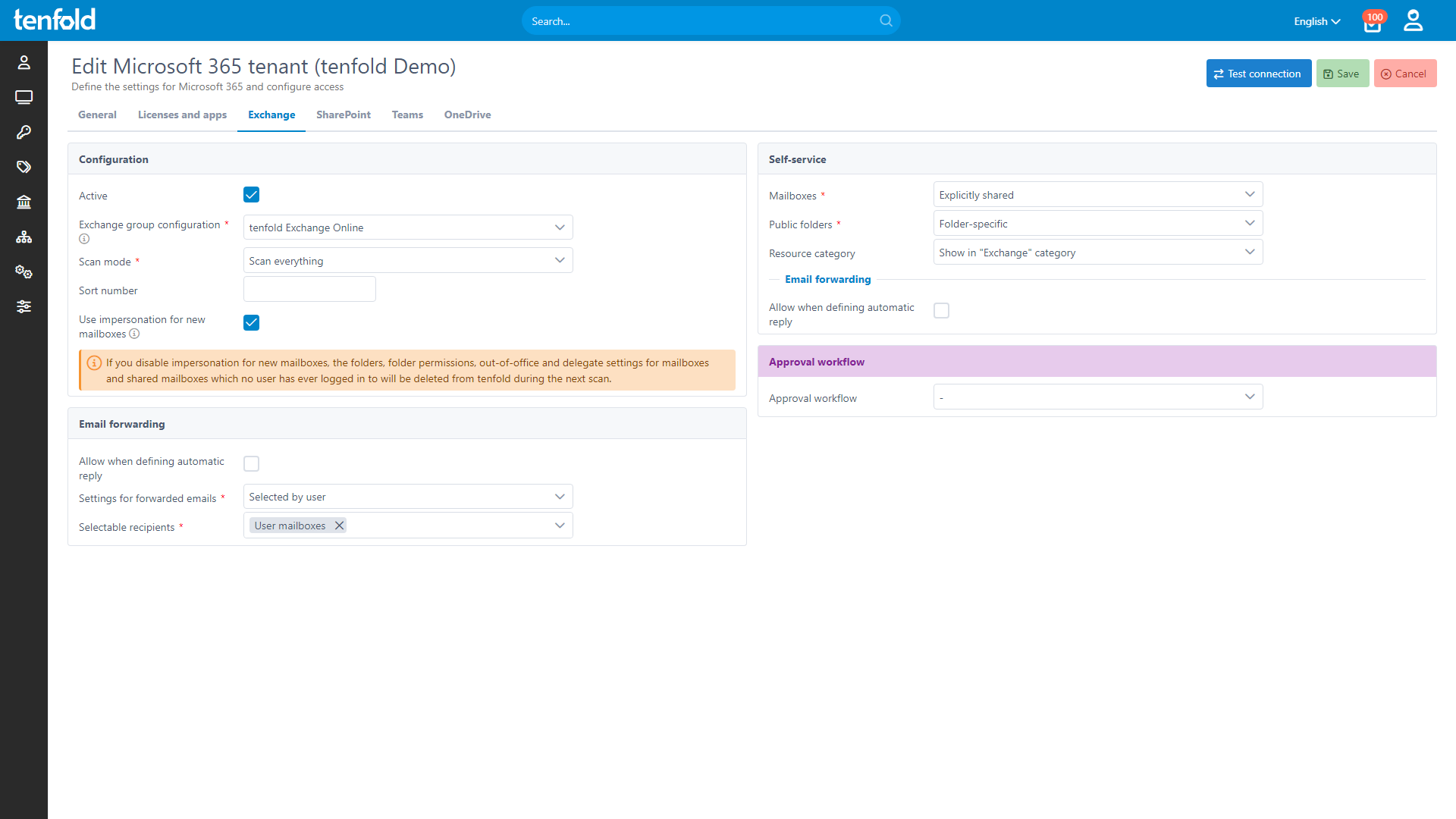
Thanks to its user lifecycle management, tenfold is able to assign and update permissions fully automatically. Users can also request additional permissions through a convenient self-service interface. Learn more about the mailbox lifecycle in tenfold.
Note: tenfold‘s Exchange plugin covers Exchange Server as well as the Microsoft 365 service Exchange Online. By interfacing with both local Windows infrastructure and the Microsoft Cloud, tenfold is able to offer automated permission management for local, cloud and hybrid environments.
Essentials 365 Edition
System Requirements:
You must have a service account with the appropriate privileges to create, move, and deactivate mailboxes.
Changes are made using the PowerShell cmdlets for Exchange provided by Microsoft. They must be installed.
You must install the tenfold Agent in order to run the PowerShell scripts on the server.
Features
tenfold allows admins and data owners to assign permissions.
Permissions can be assigned for all types of mailboxes and individual mailbox folders.
Shared mailboxes and public folders can be included in the self-service interface, where users can request additional resources.
Organizations can define data owners and approval workflows for mailboxes. This allows departments to manage mailbox access semi-autonomously.
Inheritance and nested groups are broken down to show effective permissions.
Clear overview of who has access to a specific mailbox or mailbox folder.
Detailed user-level permission reporting.
See which mailboxes and mailbox folder a specific user can access.
Ability to set out-of-office messages for other users (such as team members).
Establish company wide-templates for automatic responses.
tenfold in a Nutshell
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.