What Does the Groovy Plugin Do?
tenfold’s Groovy plugin allows you to react flexibly to events with your own Java-based scripts. This means that you can modify tenfold’s internal processes to expand certain standard features and adapt them as needed.
In addition, the plugin can be used to provide user-defined IT resources. For example, you can use a script to access an SQL database to read or write data. Alternatively, SOAP or REST web services can be addressed to exchange information with other systems.
LDAPS can be used to access LDAP directories outside the other directories, which are supported out-of-the-box. You can also create individual Word, Excel or PDF files as templates for workflows.
Essentials Edition
System Requirements:
Apart from a functioning tenfold application server, there are no special requirements.
The specific requirements of the individual target systems and the restrictions of certain APIs still apply.
Features
Scripts can be executed in response to certain system events.
Provisioning of resources via scripts is also possible.
tenfold’s internal processes via ISM Java-API
all SQL databases (Microsoft, Oracle, IBM DB/2, Informix, MySQL, etc.)
REST APIs
SOAP APIs
LDAP and LDAPS
Creation of individual file imports and export jobs
Creation of individual Word, Excel or PDF files, based on templates
tenfold in a Nutshell
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
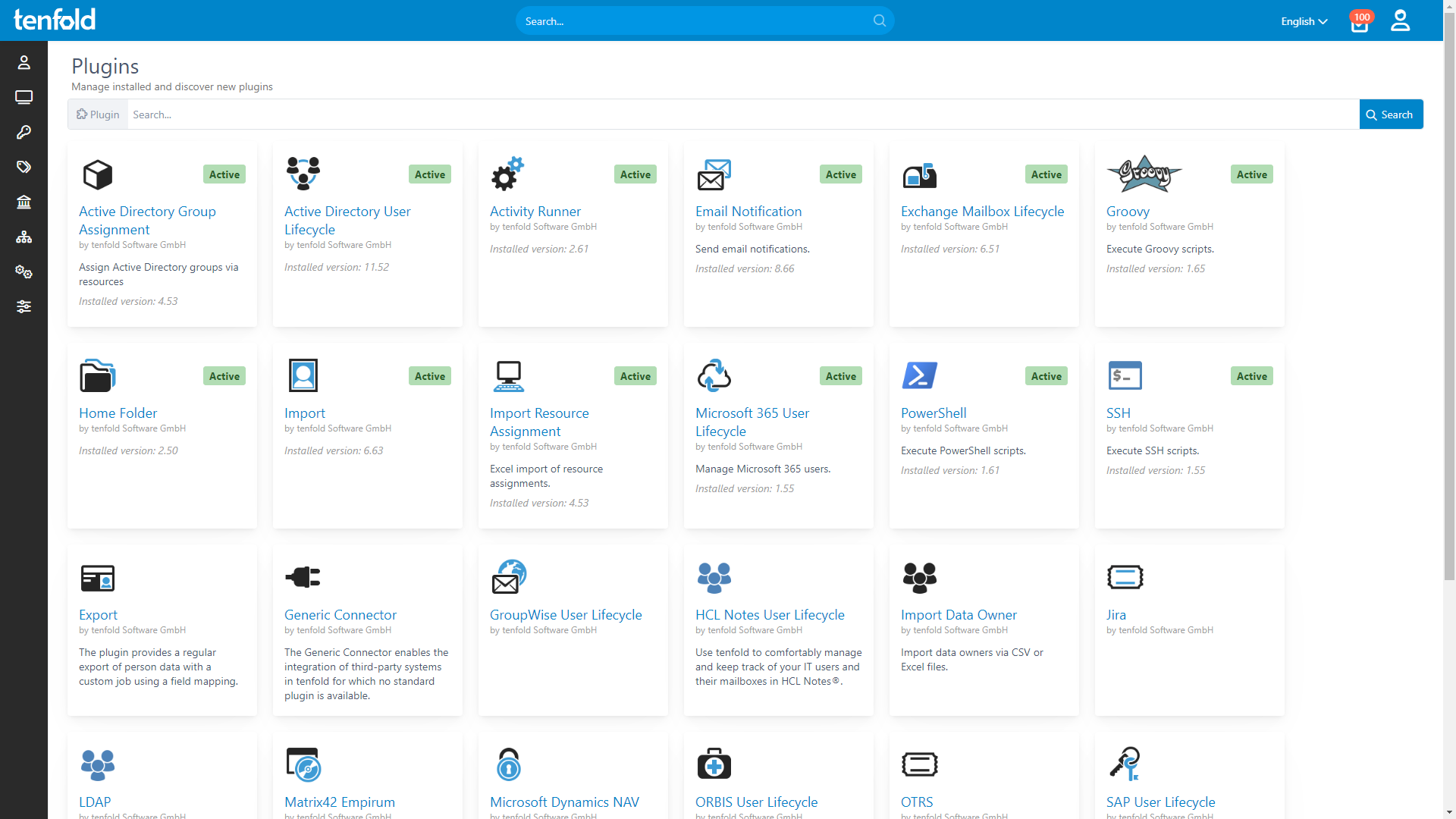
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.