What Does the PowerShell Plugin Do?
The Windows Server (or other Windows products) PowerShell extensions can be used to address or change Active Directory objects, or even to carry out more complex procedures, like the rolling out of software to client devices.
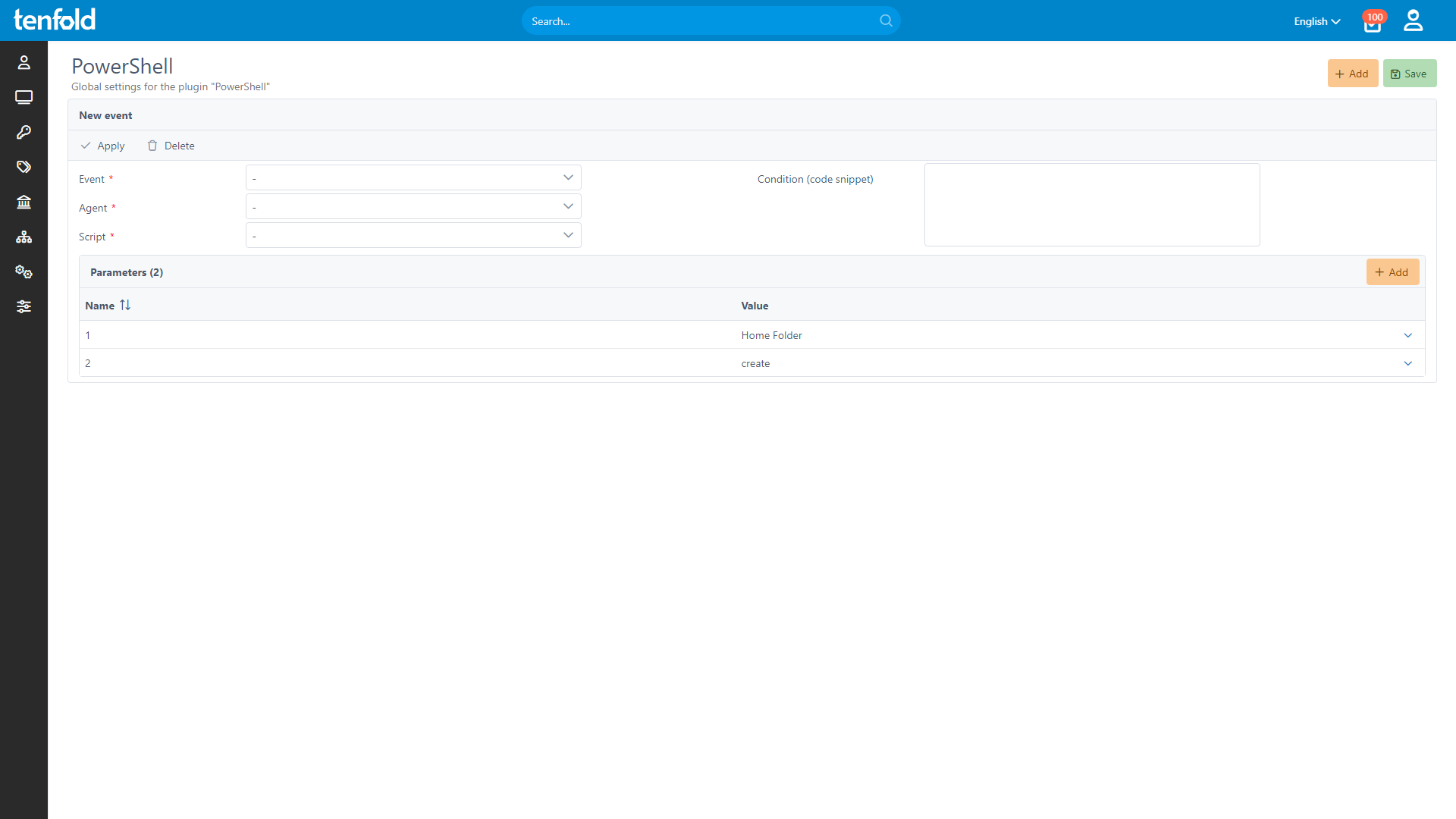
The scripts are executed via the tenfold Agent, which must be installed on one of the supported operating systems in advance. The scripts can be conveniently uploaded via the tenfold web interface and are stored in the database.
As soon as the script is to be executed, it is transferred to the respective tenfold agent in encrypted form, which then executes the script in a specially created session.
The “Import session” command triggers a remote session through which scripts can be executed on servers other than the one the tenfold agent is installed on.
Note: Many Microsoft services can be connected to tenfold via pre-built plugins, which allows changes to be made in the target system without the use of PowerShell scripts.
Enterprise Edition
The Essentials and Essentials 365 editions of tenfold allow limited use of the PowerShell plugin.
System Requirements:
All required extensions (Cmdlets) must be loaded and available
All currently available versions of PowerShell are supported.
Limitations
Some of the PowerShell plugin functions are limited in the tenfold Essentials and Essentials 365 Editions. You can, for example, run scripts for global events, such as the automatic generation and configuration of a terminal server profile path after a user has been created.
However, it is not possible to use the PowerShell plugin for resource provisioning in these editions, as only the Enterprise Edition enables user-defined resources. Note: items that are represented as resources in tenfold include business applications and access rights.
If you are unsure whether you will be able to use certain features of the plugin due to the limitations outlined above, please contact one of our partners or send us a message to: info@tenfold-security.com.
tenfold in a Nutshell
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.