What Does the SPI ISAS-N Plugin Do?
This plugin enables the ISAS-N banking system to be integrated into tenfold’s automated user and access management system, allowing tenfold to create new identities and profiles in SPI ISAS-N and to automatically assign them to the correct roles and policies, depending on previously defined access profiles. tenfold can thus also remove rights if the status of a user changes.
tenfold helps organizations to manage user accounts and access rights efficiently, while at the same time reducing the likelihood of human errors. As all changes are thoroughly logged, audits become a walk in the park.
Enterprise Edition
System Requirements:
ISAS-N Version 11.00.03
Features
Create identities and profiles
Modify personal master data in identities and profiles
Remove identities and profiles
Add roles and policies to identities
Remove roles and policies from identities
Control maximum order sums
Integration via REST web service via JSON
Secure connection via HTTPS
tenfold in a Nutshell
Complete Visibility
Gain full insight into access rights – from individual files to system-level oversight.
Centralized Governance
Govern access in Active Directory, Microsoft 365 and beyond through a single platform.
Fast Implementation
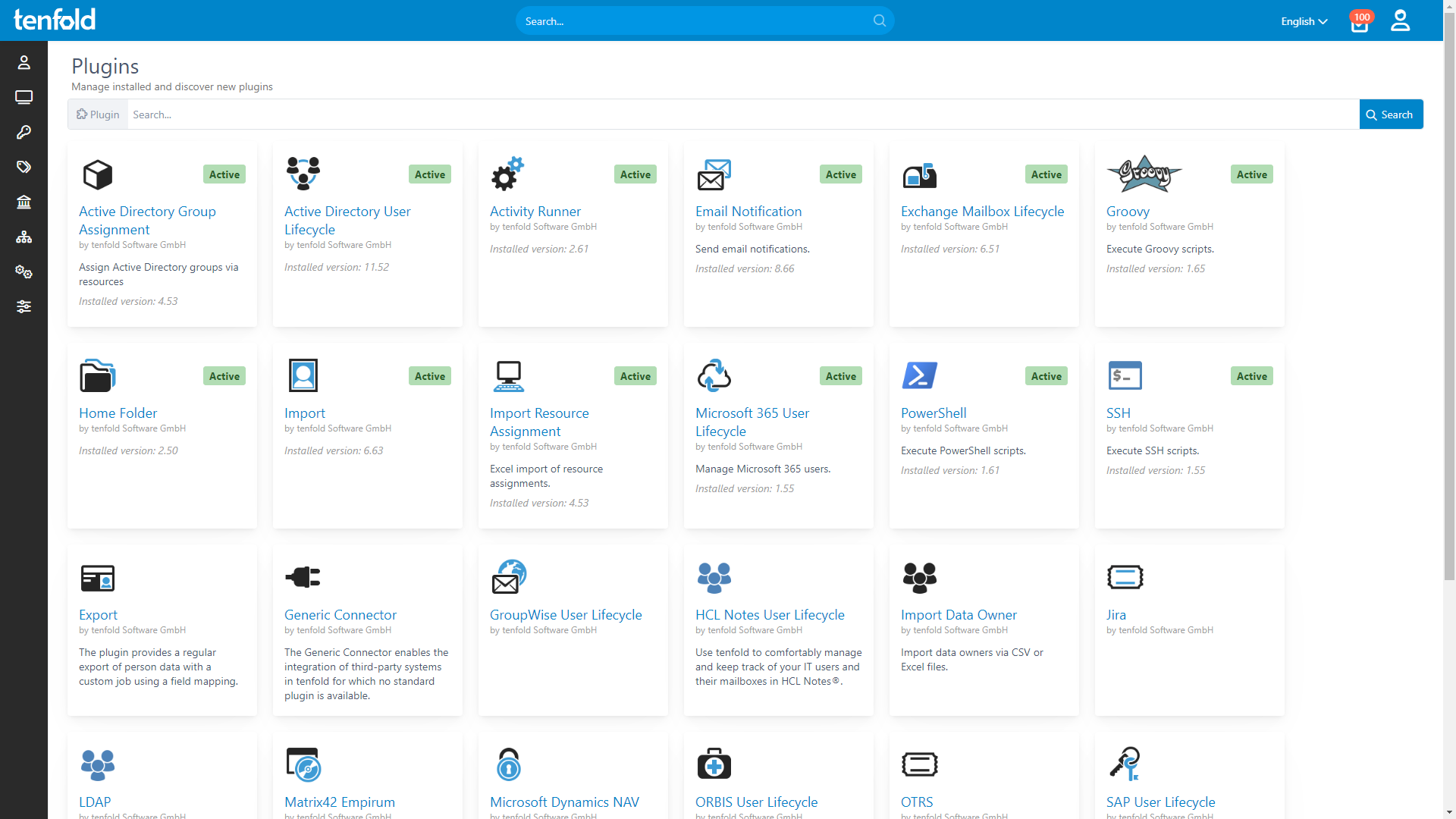
Achieve complete integration faster with our no-code platform and off-the-shelf plugins.