What’s the Difference Between Authentication and Authorization?
When it comes to account protection and IT access control, authentication and authorization go hand in hand. Although the two terms are closely linked, their exact relationship and the difference between authentication and authorization are crucial to understanding the role they play in cybersecurity.
Authentication vs. Authorization
Authentication describes the process of verifying a user’s identy, i.e. confirming they are who they claim to be. The most common form of authentication is through a combination of username and password. However, since this method can be easily fooled, many logins now require additional verification in the form of multi-factor authentication.
Authorization refers to assigning a user the correct level of access once their identity has been confirmed. After a successful login, the system checks which permissions are linked with the user’s account and makes sure they can access the intended resources (like different directories on the file server).
The difference between authentication and authorization can be summarized like this:
Authentication confirms who a user is, authorization determines what they can do.
Crucially, authentication always comes first. Only when a person can prove their identity are they given access to the resources associated with their account. Otherwise, there would be no way to prevent unauthorized access from bad actors like hackers, cybercriminals and even insider threats. You can think authentication and authorization like showing your ID to airport security. First, they check if the information matches (authentication). Then, they let you through (authorization).
How Does Authentication Work?
Identity verification can take many forms and several stages, but generally relies on comparing information provided by the user to stored credentials on a server. Since login information is very valuable to hackers, services must enforce strict cybersecurity to prevent stored data from falling in the wrong hands. This includes measures to obfuscate credentials both in storage and in transit through methods like encryption and password hashing.
Nowadays, authentication methods are grouped into tiers depending on how many security checks they include:
Single-Factor: Users have to pass a single security check, typically entering their username and password.
Two/Multi-Factor (2FA/MFA): Users have to pass multiple security checks through the use of one-time passwords, email codes, authenticator apps, biometric data etc.
To save users from having to go through this process every time, services can remember you are logged in by storing session cookies or tokens. Applications can even share authentication with other services. In this case, the confirmed identity of the user is transferred through protocols such as OAuth or Kerberos. Take for example the way websites let you sign in with Google or Facebook. Or how you only have to log into Microsoft 365 once to access different apps like Teams, OneDrive and Outlook
How Does Authorization Work?
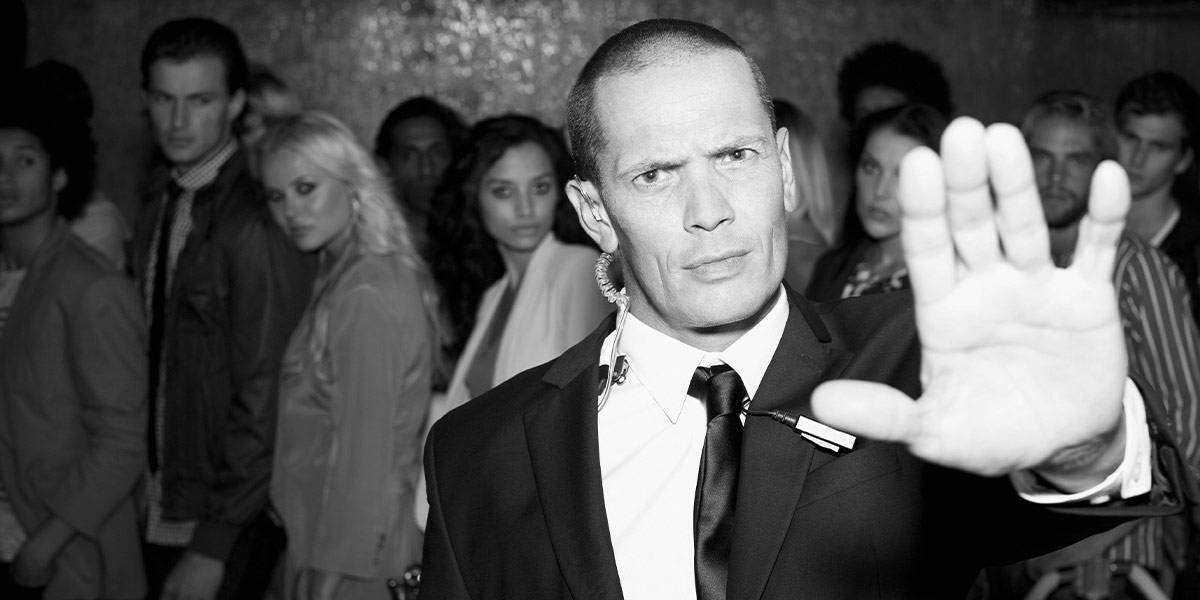
Again, there are many ways to authorize users once you have verified their identity. Authorization in Windows and most operating systems relies on Access Control Lists or ACLs. Put simply, each Windows object has a list of Security Identifiers that are either allowed or explicitly denied access. When you try to open a shared folder, Windows checks your account ID against this list like a bouncer making sure you’re allowed into an event.
To authorize a user on a particular directory, admins can open the settings for this folder and add them to the list. However, this is a really ineffcient way to manage NTFS permissions. Authorizing individual users can work for a smaller organization, but quickly becomes a problem when you’re dealing with dozens or hundreds of accounts.
In practice, authorization in Windows environments relies on Active Directory groups which grant permissions on a specific resource to all of their members. Using group membership for access control has the advantage that any changes you need to make only require a single edit to one group instead of dozens of individual accounts or objects. This is especially true if you follow Microsoft’s best practice of nesting groups through the AGDLP principle.
Authentication and Authorization Across Multiple Systems
So now we know how to authenticate and authorize a user in Windows: They log into their account and can then access any resources that their security ID is approved for. But what about other applications they may want to use, like cloud storage, creative tools, helpdesk systems, HR software and so on? Since all of these systems maintain separate logins and permission lists, managing access requires admins to update accounts individually in each service.
This is where identity and access management comes in: Thanks to a wide range of plugins, IAM solutions act as a central hub for managing accounts and access rights across your entire IT infrastructure. They allow you to set the intended level of access in all connected apps from a single location. But more than that, IAM allows you to automate the entire process from account creation to regular user access reviews.
Centralized Access Control
To achieve this level of automation, identity and access management software relies on efficient and centralized models like role-based access control. Under this system, organizations define roles containing the intended permissions for users in different positions and departments. Of course, this must be done in accordance with the principle of least privilege. When a user is added to one of these roles, the IAM platform assigns the correct privileges in all connected applications.
At the same time, IAM solutions remove any permissions that are not part of this agreed-upon set. This is critical in order to prevent privilege creep, the gradual accumulation of privileges as users move through different roles and departments.
The baseline of access rights assigned through role-based access control can be further expanded or restricted through flexible methods of user authorization. For example, models for conditional access take into account various factors and context cues to determine whether an action should be allowed. This includes the location and device of the user, which action they are trying to take (read, edit, delete etc.) and how sensitive the target file has been marked as.
Access Governance Best Practices for Microsoft Environments
Everything you need to know about implementing access control best practices in Active Directory, from implementation tips to common mistakes.