Empower Departments to Grant Access, Eliminate IT Bottlenecks
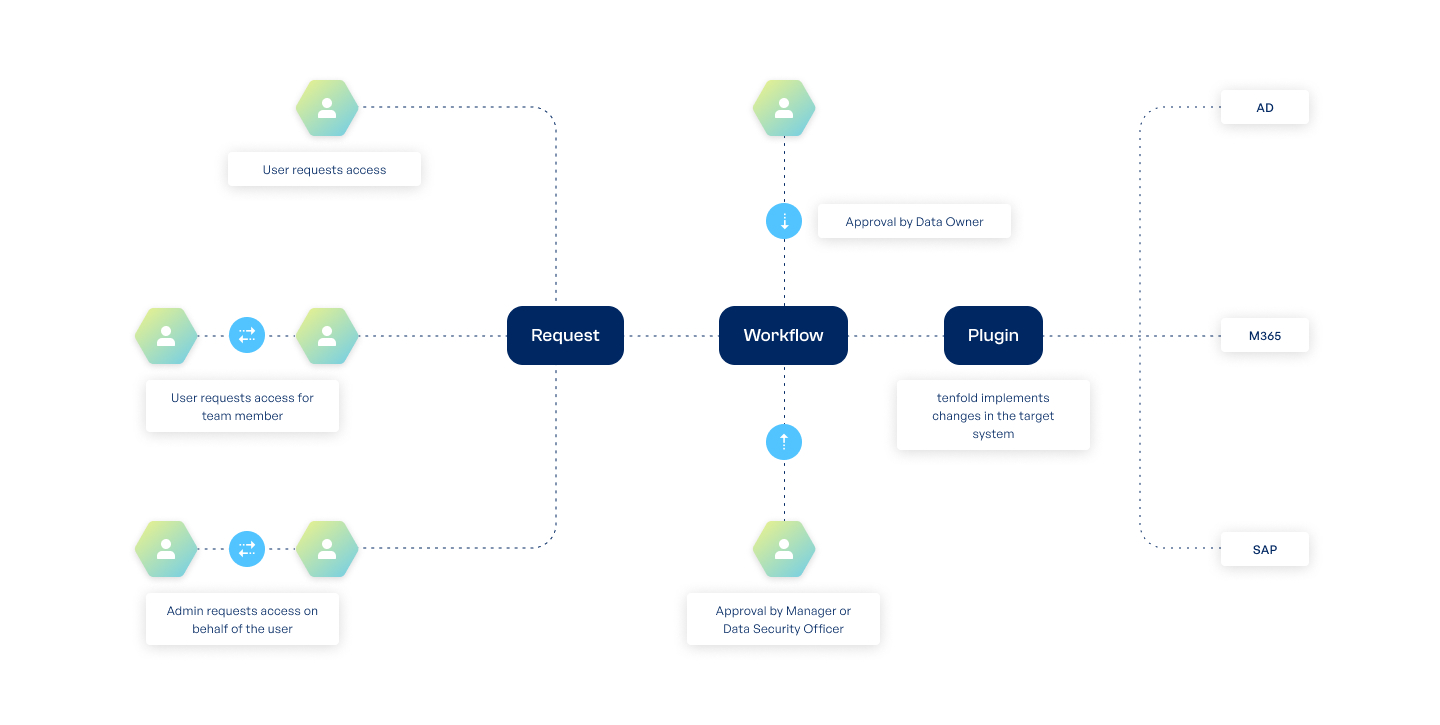
tenfold’s self-service platform allows data owners within departments to manage routine access requests independently, reducing IT workloads and ensuring users receive access faster. This streamlined process improves operational efficiency while maintaining security.
Help Your IT Focus on High-Impact Tasks
Helpdesk tickets can slow down IT productivity.
tenfold’s self-service workflows empower users to resolve common access issues independently, allowing IT to focus on critical initiatives.
Empower Your Users
Allow on-demand access requests
Simplify license or hardware requests
Offer secure, self-serve password resets
Accelerate Approvals
Assign data owners to manage requests
Leverage a visual workflow editor
Support flexible, multi-stage approvals
Maintain Control
Decide who can request which resources
Track all requests with detailed logging
Enforce identity verification for requests
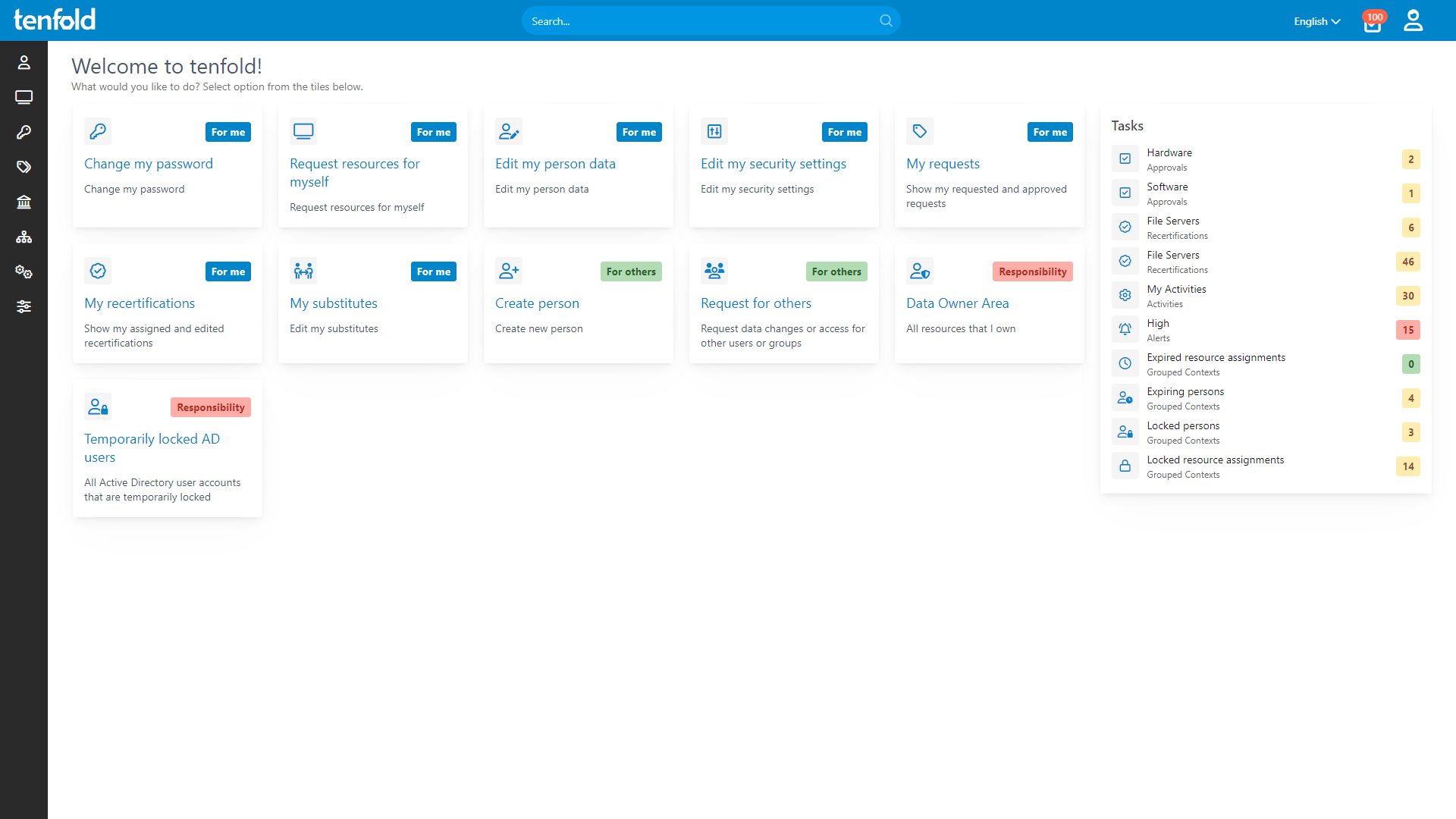
Intuitive User Interface
tenfold’s easy-to-use web interface simplifies the request process for users of all experience levels, allowing them to quickly request access or reset passwords without IT intervention.
Custom Workflow Editor
Design and automate approval workflows with a visual BPNM editor, supporting complex logic like branching decisions, escalations and fallback processes to meet your specific organizational needs.
Seamless ITSM Integration
For workflows that require manual steps, such as hardware provisioning, tenfold integrates with ITSM platforms to automatically create and track tickets, streamlining your IT service management.
%
75
Lower IT Workload
%
95
Faster Access Provisioning
%
98
Recommendation Rate on Capterra
%
100
Privilege Creep Reduction
Why Choose tenfold?
tenfold’s quick setup, easy configuration and powerful features make it the ideal choice for anyone looking to securely manage user accounts and IT privileges. Our all-in-one solution combines identity and data access governance into one convenient and user-friendly package.
Download our IAM Comparison
Ready to Try It Yourself?
Cloud Demo Environment
We give you acces to a cloud environment prepopulated with users and a ready-to-go tenfold instance.
Start testing right away
Enjoy our no-code UI and easy configuration
Try our automated workflows in a sandbox environment with prebuilt users & groups
Full access to all of tenfold’s features
7 day trial period
Proof-of-Value Installation
Our consultants help you set up tenfold on your network so you can test it against your own infrastructure.
In-depth test in your own IT environment
Try our no-code plugins and integrations
Turn your demo install into a real deployment (No lost work!)
Full access to all of tenfold’s features
30 day trial period
Frequently Asked Questions
tenfold‘s self-service platform can be fully customized to display different menu items to different groups of users. The full range of accessible features includes requesting new permissions or hardware resources as well as the option to review pending requests, edit your own user data or assign delegates. Users in leadership roles can also manage certain settings for their team members.
To help you create new approval workflows, tenfold provides an easy-to-use, graphical editor based on BPMN 2.0. With a few simple clicks, you can customize the data owner in charge of a given resource, the time limit for answering requests and fallback actions for unanswered requests. Options for escalating unanswered requests include email reminders as well as forwarding the request to supervisors.
Important: Workflows are not tied to a specific person, but the data owner role. If the data owner in a department changes, existing workflows are automatically updated. There is no need for manual changes.
Many organizations task their IT department with assigning any new permissions, but admins have to assess these requests at a distance and often lack critical context. Putting department leaders in control of their own data makes decisions about access both faster and more accurate.
All you have to do is define a data owner for certain parts of your network and tenfold takes care of the rest. When a user requests access to a resource under their control, data owners are automatically notified via email and can immediately grant or deny the request. To prevent misuse, data owners must verify their identity using MFA or Kerberos tokens.
Once a request has been approved, tenfold grants access to the user, documents the data owner’s decision and adds the new permission to the next access review.
To help process access requests quickly, tenfold allows you to assign delegates for data owners. Should a data owner be unavailable due to illness, travel or personal reasons, requests are forwarded to their delegate. You can also set a successor for the data owner position to ensure a smooth transition. Since workflows in tenfold are not tied to specific users, you can change data owners without having to edit existing workflows.
The self-service password reset feature supports all applications in which you manage user data through tenfold. This includes the Windows Active Directory password, as well as many cloud services and third-party solutions. Check our plugin overview for more information.
Take the Next Step
See tenfold in Action With Our Feature Video
Schedule a Live Demo With One of Our Experts
Put tenfold to the Test With Our Free Trial!