What Is Data Access Governance (DAG)?
Data is at the forefront of our increasingly digital economy. This makes governing and controlling access to data an essential capability for modern enterprises. Solutions for data access governance (DAG) provide organizations with the means to track and manage access to sensitive information in-depth.
Three key takeaways:
Data access governance offers in-depth control over data access, while identity governance takes a bird’s-eye view of user roles and permissions.
The core capabilities required for data access governance are centralized reporting, access control/remediation and recurring access reviews.
The built-in DAG features of systems like AD and M365 are insufficient, driving the need for dedicated data access governance solutions.
What Is Data Access Governance?
Data access governance or DAG refers to a mix of policies, processes and technologies that allow companies to control which data their staff can access. For a modern enterprise to function effectively, employees need seamless access to all sorts of information. At the same time, businesses need to protect sensitive data from unwanted and unauthorized access.
Security experts refer to this balancing act as the principle of least privilege: users should have access to all the information they need to do their job, but nothing beyond that. Least privilege is an essential component of modern security strategies like zero trust and data access governance provides the oversight needed to implement this crucial strategy.
Unlike access management, which focuses on high-level decisions like adding users to apps, groups, channels or directories, data access governance goes in-depth on what exactly each user can access, down to individual files or documents shared in the cloud.
What Is Unstructured Data?
Most information that companies keep is stored as unstructured data. So, to understand the challenges of data access governance, it’s important to first understand what exactly unstructured data is.
Unlike structured data, which is stored in databases and formatted to be easily machine-readable, unstructured data comes in a wide variety of file types and formats: text documents, images and videos, audio recordings and many others. Unstructured data represents the vast majority of information that humans create and interact with.
However, the disorganized nature and sheer volume of unstructured data makes it challenging to secure. Unlike a clearly structured database, you can’t really tell what kind of information might be buried in a text file. It could be notes from a meeting, sensitive financial data, confidential strategy or anything in between.
Why is Data Access Governance Important?
When it comes to data access, the devil is in the details. While it’s important to maintain a big picture view of which apps and areas of your network different users can access, the only way to know what’s really happening to your data is by tracking access on an object and user level. Without the kind of fine-grained view provided by data access governance, you’ll miss important and potentially dangerous events.
Let’s go through an example: Say your Human Resources department has a dedicated channel in Microsoft Teams. Two members of the team, Alice and Bob, are tasked with planning the next company party. To help them create invitations, they bring in Charlie, a member of the Design team. They add Charlie to the HR channel so he can view their timetable and planning document.
But there’s a problem: Now Charlie also has access to all the other files uploaded to the channel, including spreadsheets that contain sensitive personal information. Data that no one outside of HR should have access to. And yet all of this happened without any security alerts being triggered. The Head of HR was never even notified of a new user being added to their Teams channel.
How Does Data Access Governance Work?
There are three main components to data access governance, which are also the core features of any DAG solution:
Centralized reporting: Businesses store and process in a wide range of different systems. The diversity of tools available to modern enterprises has many advantages, but it makes critical data increasingly difficult to govern. Especially since most of these apps lack detailed reporting capabilities of their own. By providing a central overview of user access across their entire IT stack, DAG offers the visibility you need to combat this problem.
Access governance: Remediating unwanted permissions is important, but it’s better to make sure users do not receive them in the first place. Through policies, lifecycle automation and access control models like role-based access control, governance solutions allow organizations to make sure their users receive the exact privileges they need for their job.
Access reviews: With business needs and user responsibilities changing over time, the only way to ensure safe and appropriate access long term is to regularly audit IT privileges. User access reviews, carried out by the data owners you assign to various IT assets, allow you to identify and remove outdated permissions such as guest access left active after a project has ended.
5 Best Practices for Effective Access Reviews
Data Access Governance: Additional Features
Apart from these three main pillars of data access governance, there are many additional features and capabilities that DAG platforms might offer. Many of these overlap with related software categories such as data security platforms or data security posture management (DSPM).
While these components are not required for data access governance, they may be useful additions depending on your specific security needs.
| Feature | Definition |
|---|---|
| Automated Discovery | Discover files and other information assets across different IT systems to ensure all data is managed securely. |
| Data Classification | Identify files containing sensitive information like SSNs, label them accordingly and apply policy based on sensitivity levels. |
| Real-Time Monitoring | Track which files your users are accessing in real time to protect critical data from unwanted access. |
| User Behavior Analytics | Observe user behavior to detect suspicious activity, early signs of a possible breach or account takeover. |
| Data Loss Prevention | Prevent employees from leaking sensitive information by limiting sharing options and encrypting critical data. |
| Data Masking | Enable secure sharing assets by automatically masking sensitive information like account numbers or personal data. |
Data Access Governance and Regulatory Compliance
Aside from the security benefits of preventing employee data theft and minimizing the risk of data breaches, data access governance is also required by law in many situations.
Depending on where your business operates and what kind of data you process, there are various regulations you may be forced to comply with. For example, the GDPR, GLBA and HIPAA all require covered entities to limit who can access personal information.
Of course, there are many other industry and region-specific standards to consider, as well as voluntary cybersecurity certifications like NIST CSF, ISO 27001 or the CIS Controls. No matter which regulatory challenges you face, DAG is a central to overcoming them.
Data Access Governance in Practice: Securing Cloud & On-Prem Environments
Despite the importance of effective data access governance, many organizations choose to forego a dedicated DAG solution and rely exclusively on manual administration and the built-in capabilities of different IT systems.
Unfortunately, the default tools available in systems like Active Directory or Microsoft 365 are simply not up to the task of providing a clear overview of user access to data, let alone effective governance of critical information.
To highlight the challenges of managing data access across these different platforms, we’ll briefly introduce you to their built-in DAG features, explain their shortcomings and outline the need for more sophisticated tools.
Data Access Governance in Active Directory
The Problem: Limited Visibility
The biggest challenge with data access governance in Active Directory domains and Windows file servers is a lack of transparency. Here’s the problem: Explicit permissions, i.e. permissions set directly on an object instead of through an AD group, are not visible when you check a user’s account. They only show up if you check the file or directory in question. With thousands of files and folders, that means explicit permissions are effectively invisible.
Possible Workarounds
There are some ways you can track down explicit permissions in Active Directory, from utilities like AccessEnum to using the PowerShell cmdlet Get-Acl to search for entries in the Access Control List that have not been inherited. But this approach only works if you already know there’s a problem.
By contrast, a DAG solution automatically keeps track of all permissions and highlights problematic access as soon as it happens. This takes the guesswork out of securing sensitive data in your AD domain.
Best Practice Security
The good news is, you can mitigate the problem of limited visibility in Active Directory at least somewhat by following best practices for Active Directory permissions. Always assign permissions through groups, follow the AGDLP principle to model role-based access control, focus on the top levels of your folder structure and let inheritance handle the rest.
However, your security strategy shouldn’t rely on everything going according to plan. Sooner or later, one of your admins is going to slip up and grant a user direct access to a folder – whether it’s due to time pressure, convenience or a straight-up mistake. So how do you identify and fix these permissions before they become a problem?
Access Governance Best Practices for Microsoft Environments
Everything you need to know about implementing access control best practices in Active Directory, from implementation tips to common mistakes.
Data Access Governance in Microsoft 365
The Problem: Uncontrolled File Sharing
The ability to easily share documents you’re working on through apps like Teams, OneDrive and SharePoint is one of the biggest selling points for cloud collaboration platforms like Microsoft 365. But while sharing documents certainly boosts productivity, it also makes it a lot harder to track who has access to which files.
Much like Active Directory, the main problem with data access governance in Microsoft 365 is that there is simply no visibility into who has access to specific files. Has it been uploaded to a channel? Are there guest users on that team? Has the link been shared? Who received it? Who opened it?
Global Restrictions for External Sharing
At least when it comes to external sharing, M365 gives organizations some options for stopping unwanted behavior. Orgs can choose between four settings to limit external sharing: disabling it entirely, limiting it to known guests, requiring new guests to authenticate through an email code or allowing unrestricted sharing.
Unfortunately, there are two problems with these org-wide restrictions:
Internal sharing is just as likely to lead to problematic access as external sharing.
Most businesses do not want to block sharing outright, they simply want better oversight over what information their users are sharing and with whom.
Entra Permissions Management
With recent changes to the Azure AD/Entra ID product family, Microsoft has introduced new paid addons to support compliance and identity governance in the cloud. Two notable additions in this category are Entra ID Governance, which supports lifecycle workflows and access reviews, and Entra Permissions Management, a CIEM solution for identifying unused cloud privileges.
So, does that mean the problem has been solved? Unfortunately, both Entra ID Governance and Entra Permissions Management focus on high-level privileges: access to specific apps, membership in M365 groups or built-in roles like App Developer, Global Reader or Teams Administrator. These solutions don’t tell you which files your users can access in the cloud.
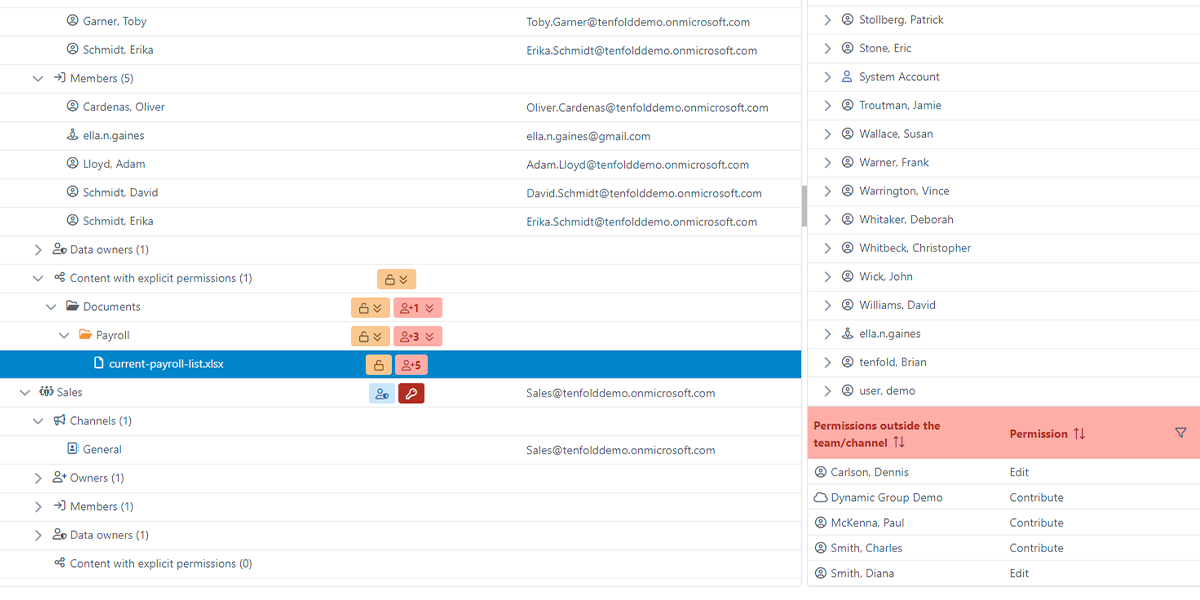
Unlike these tools, tenfold gives you a clear breakdown of shared files – highlighting access outside the channel and outside the organization.
But that doesn’t mean you miss out on high-level governance: Our all-in-one solution combines identity lifecycles and automated provisioning with in-depth reporting and access reviews.
Access Governance in M365: Best Practice Guide
Everything you need to know to manage cloud privileges in Microsoft 365 – from built-in tools to essential best practices!
tenfold: IAM meets Data Access Governance
With data controlling more and more of our lives, control over data becomes an essential capability for enterprises that want to succeed in modern, digital markets. But data access governance is far from the only challenge businesses face. To secure mission-critical information, enterprises need to effectively govern high-level privileges as well as object-level permissions.
That’s why tenfold combines the automated lifecycle management of identity and access management with the in-depth reporting and fine-grained access reviews of a data access governance platform. And the best part? As a no-code solution, tenfold can be deployed significantly faster than similar tools. Don’t leave secure access up to chance! Take control of your data with tenfold.
Our No-Code Solution Makes IAM Easy.
Start Your Free Trial Today!